Coupa Treasury Agility Starts with Visibility - Take Treasury to the Next Level
Explore Coupa Treasury
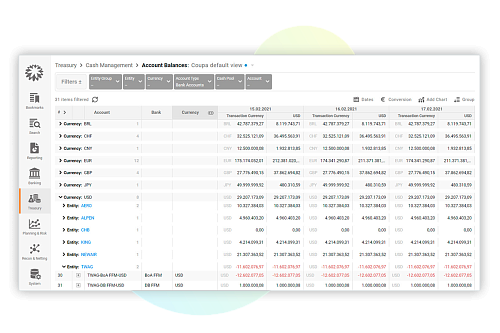
Quickly and Easily Act on Cash Insights
Coupa delivers complete, real-time visibility and transparency for organizations with multiple subsidiaries, currencies, and accounts. Instantly know your cash position, move funds with one click and run scenarios to see how long funding will last if income or expense categories are adjusted.
Manage Short- and Long-Term Instruments
Manage all debt and investment positions in Coupa’s single control center. Stay on top of maturities, interest and principal settlements, as well as risks across all banking partners, your in-house bank, and other counterparties. Streamline processes by automating transactions, accrual and valuation accounting.
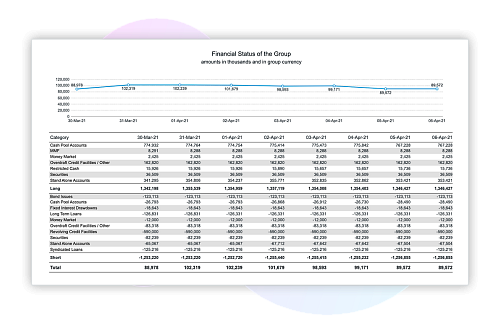
Smarter Cash Flow Forecasting
Boost confidence in short, mid and long-term business health with Coupa’s cash forecasting and liquidity planning capabilities. Draw numerous scenarios, versions, workflow management, group consolidation, actual vs. plan analyses, intercompany forecast reconciliation and much more.
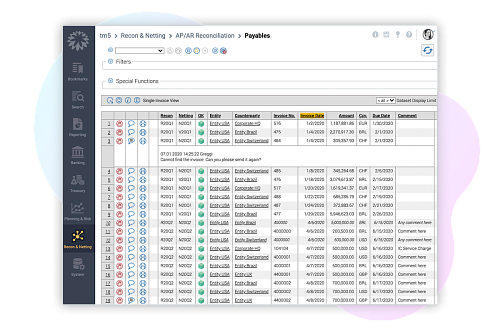
Save Big With Intercompany Netting
Lighten workloads with multilateral netting powered by Coupa. Transparent and automated reconciliation and netting of intercompany invoices reduce transactions and costs while optimizing internal financing, cash allocation and hedging risks.
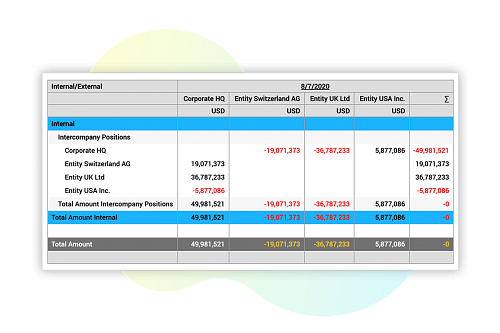
Capitalize on In-House Banking
Be your own best banking partner. Consolidate subsidiary exposure and streamline intercompany transfers with centralized group-wide payments, cash pooling and simple intercompany account structures for all subsidiaries. Optimize intercompany financing and hedging.
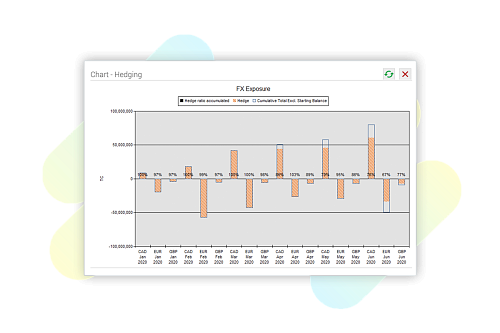
Identify and Mitigate Financial Risk
Make use of actionable, real-time data and integrated trading platforms to document, manage and evaluate deals and trades. Protect against FX risk and interest rate volatility and perform scenario and sensitivity analyses with ease. Exposure and hedge ratio tracking ensure compliance.
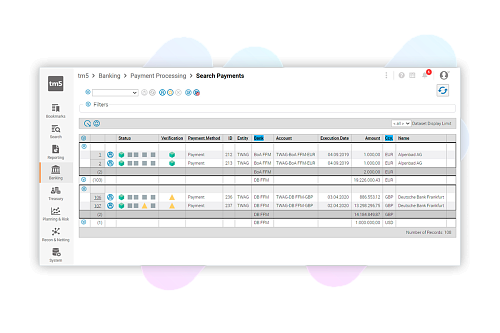
Bank Connectivity with Comprehensive Payment Management
Designed for maximum control and agility, Coupa provides a multi-banking portal with universal accessibility for global, domestic and ERP invoice payment processing in a secure environment. Set up automated payment runs to boost efficiency and shore up your fraud defenses.
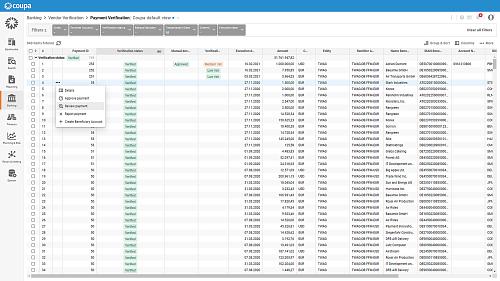
Ensure Compliance and Prevent Fraudulent Payments
Rely on Coupa for compliance with regulations, secure processes and a full audit trail. Minimize the risk of payment fraud with integrated risk mitigation, payment verification and artificial intelligence. Detect suspicious activities with a central vendor database and streamline payment approval using validation status.
Analyze and Share Meaningful Data
Drawing conclusions and delivering insight hinges on a team’s ability to interpret data easily and quickly, share financial data and keep the organization agile. With Coupa's comprehensive solution, you have access to flexible, standard reports as well as a custom report designer.
Easily Join and Comply with the Global SWIFT Network
Coupa helps you become a Standard Corporate Environment (SCORE) member of the most powerful and secure financial network for cash management, payments, digital matching and trade finance. Receive your own BIC and let us take care of your compliance with the Customer Security Programme (CSP) and token management.
The Power of Suite Synergy
Unlock more value from treasury and cash management with Coupa's suite of seamlessly integrated BSM applications.
+
Treasury Management + Payments
Gain complete, real-time transparency into multiple subsidiaries, currencies, and accounts for sound decision making and streamlined payments.
+
Treasury Management + Working Capital
Increase visibility from source-to-settle and automatically incorporate payments into the cash position to identify excess or deficit cash.
+
Treasury Management + Procurement
Reduce financial risk from supplier contracts and payments to protect against FX risk and interest rate volatility.
Optimizes Cash and Reduced Dependency on Banks
"We were able to save over 50% in bank fees by optimizing bank accounts."
Jeremy Hamon, Head of Group Finance, Primetals Technologies
Learn About Primetals Technologies and Coupa